News & Updates
Last week, Peace Action New York State representatives were in Washington, D.C. for #CeasefireNow Nationwide Grassroots Advocacy Days. More than 600 activists from more than 50 other peace organizations and 35 states were on Capitol Hill and in meetings around the country with members of Congress urging them to support an immediate, permanent ceasefire in Gaza; to prevent the conflict from becoming a wider regional war; to oppose further military aid and offensive weapons shipments to Israel; to require the State Department to provide a human rights report on Israel’s campaign in Gaza; and to remove the ban UNRWA aid.
This week, Peace Action New York State representatives are traveling to Washington, D.C. for #CeasefireNow Nationwide Grassroots Advocacy Days. Hundreds of peace activists from our nationwide coalition will be on Capitol Hill and in meetings around the country with members of Congress working to turn the tide on U.S. support for Israel's war in Gaza. We will be meeting with our elected representatives from New York to urge them to support an immediate, permanent ceasefire in Gaza; to oppose further military aid and offensive weapons shipments to Israel; to require the State Department to provide a human rights report on Israel’s campaign in Gaza; and to remove the ban UNRWA aid.
The annual Upstate Campus Tour kicked off on Monday, March 4th when Executive Director, Emily Rubino and Student & Campaigns Coordinator, Margaret Engel set off from NYC to visit 7 upstate campus chapters and 4 PANYS community chapters in Bronxville, Geneseo, Buffalo, Niagara, Syracuse, Potsdam, and Albany. This yearly tour around New York State is an opportunity for our PANYS state office staff to strengthen our multigenerational organizing network across the state, hear from PANYS chapter leaders about the work they’re doing in their local communities, and build connections with our student organizers who are paving the way for the future of the peace movement.
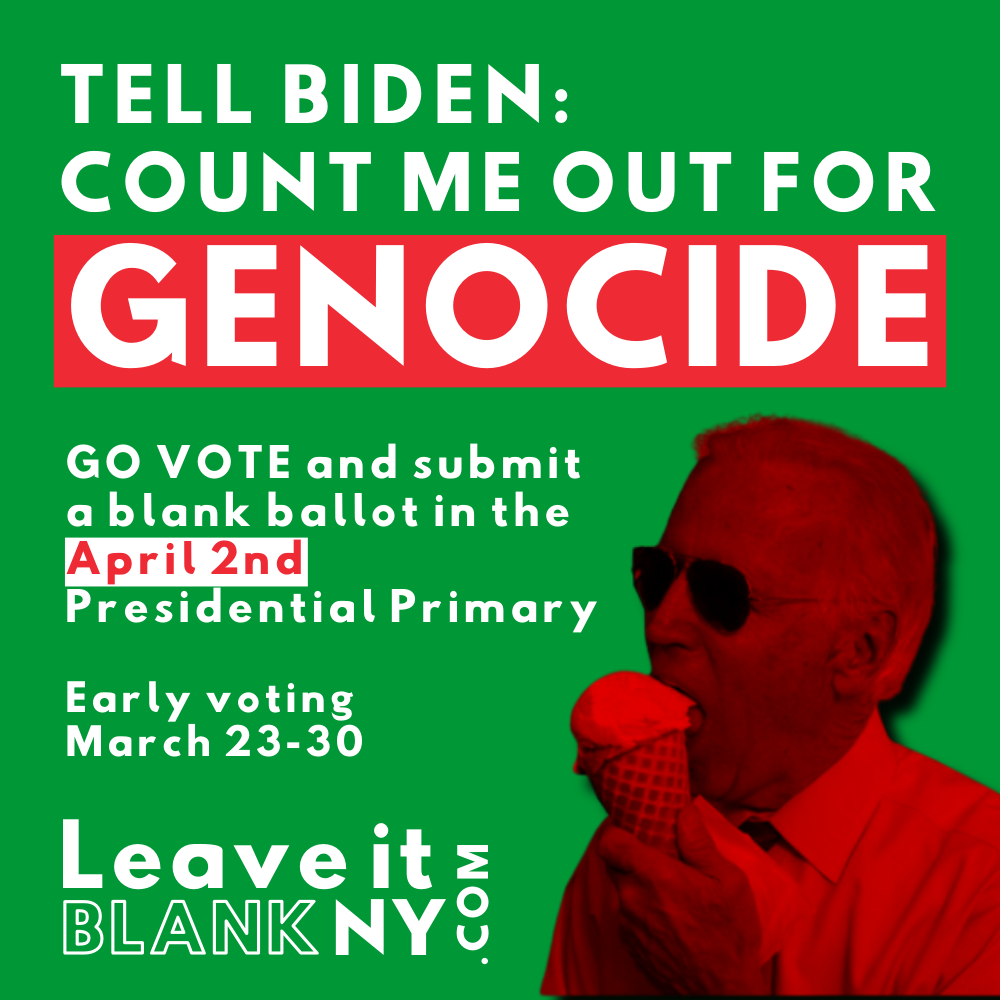
Peace Action New York State is an endorser of the #LeaveitBlankNY initiative encouraging voters to send a message to President Biden that New Yorkers want a lasting ceasefire in Gaza. The initiative encourages New York Democratic Primary voters to cast a blank ballot when they go to the polls on April 2nd.
Peace Action New York State represents thousands of peace activists across the state of New York who are organizing in their local communities to demand peaceful solutions to global conflicts. We are lobbying our local and national leaders to demand an immediate ceasefire in Gaza, a diplomatic path to end the war in Ukraine, the abolition of nuclear weapons, a reduction of the Pentagon budget, and for human needs to be prioritized over endless militarism. We are taking to the streets to educate and inform the public about these issues and how they can join us in taking action.
Read the latest news from Peace Action New York State!
The student organizers of the Peace Action Fund of New York State call on students across the state and country to stand as a united front against the U.S.-funded oppression and violence against Palestinians. We stand with other student groups in their efforts to hold academic institutions accountable for the silencing of student voices calling for a ceasefire in Gaza and an end to the continued US aid to Israel.